Authentication ≠ Transaction Security
Most banks still treat Multi-Factor Authentication (MFA) as the finish line. But modern fraud doesn’t break the login. It exploits what happens after authentication.
OTP. Push approvals. Session cookies. They prove who clicked. They don’t prove what was approved.
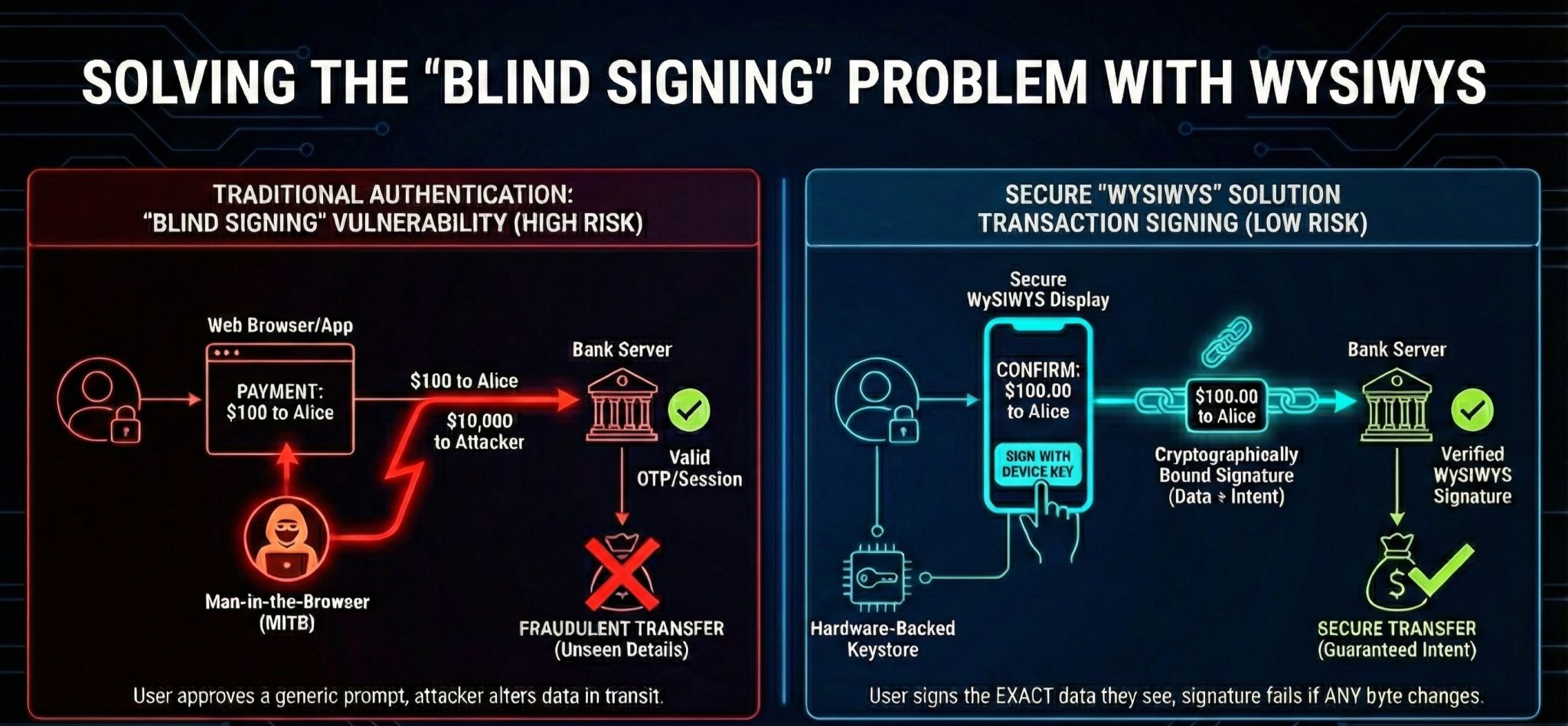
The Problem of Blind Signing
If a session is hijacked and the amount or payee is silently altered via a Man-in-the-Browser (MitB) attack, the OTP is still technically valid. The bank sees a legitimate approval, but the transaction is fraudulent.
That is Blind Signing. The user signs something—but not what they think they are signing.
What You See Is What You Sign (WYSIWYS)
Real protection requires a shift in architecture. We must move away from session reliance and toward WYSIWYS:
- Cryptographic Binding: Bind the exact transaction (amount + payee) to the signature.
- Hardware Security: Use device-bound keys stored in secure hardware enclaves.
- Immutability: Ensure the signature fails mathematically if even 1 byte changes in transit.
- Domain Binding: Enforce strict origin binding to neutralize phishing relay attacks.
The Core Difference
Authentication proves identity. Transaction signing proves intent. These are not the same problem, and they should not be solved the same way.
The future of digital banking isn’t a stronger login. It is cryptographic intent verification.